Table of Contents
Chapter 1: Introduction
SendGrid sends over 100 billion a day on behalf of paying customers around the planet. As the sender of so much of the world’s legitimate email we have to be aware of and protect our customers’ customers from a wide range of malicious messaging attacks.
Email is arguably the most widely used digital communication mechanism in use today—it is also the most abused channel because of its popularity and open nature.
When email was created in the 1970s, no one could’ve imagined the reach it has today. During the Internet’s infancy, email was a simple communication tool between academics and the inventors of ARPANET. Today, email is a driver of commerce, human interaction, and unfortunately high-profile compromises of data and systems.
Email has proven susceptible to a wide range of attacks and leveraged in more complicated fraud and other malicious campaigns. As a major driver of email traffic on the Internet, we must stay abreast of the different forms of messaging abuse and Internet fraud so that we can, from an information security standpoint, deploy appropriate counter-measures to keep bad actors off our network.
Senders of legitimate email should know and understand the kind of compromises that exist and how they can avoid behaving like spammers. This will help improve their brand’s engagement while decreasing their exploitable footprint through the application of appropriate authentication technologies.
Starting with a common lexicon and with an understanding of the perils and how to fend them off is the first step in creating a safer inbox for our customers and for email users all over the world.
Chapter 2: 419 Scam
You’ve probably received one of these—the email claims to be from a high ranking official overseas that has millions of dollars they wish to transfer to you but, they need your personal information and a small fee to facilitate the transfer. Sound too good to be true? Well it is.
The 419 scam or Advance Fee Fraud, derives its name from the section of the Nigerian penal code dealing with fraud, 419. The scam rose to prominence in Nigeria as a kind of cottage industry. Unfortunately, these kinds of scams are impossible to combat using email authentication as they are often sent person to person, from a webmail account, and using dictionary attacks to generate random lists of recipients or by obtaining the contact/address book of someone’s compromised email account.
The advance fee fraud has been around for over a decade. It isn’t a sophisticated attack, it preys on personal motivation and greed. In 2006, The New Yorker wrote an article about a psychotherapist who fell prey to one of these scams in what was then an early expose. More recently, advance fee scammers have been targeting professional conferences to obtain overseas visas by registering for events that issue invitations to participate, and help facilitate international travel.
Chapter 3: Botnet
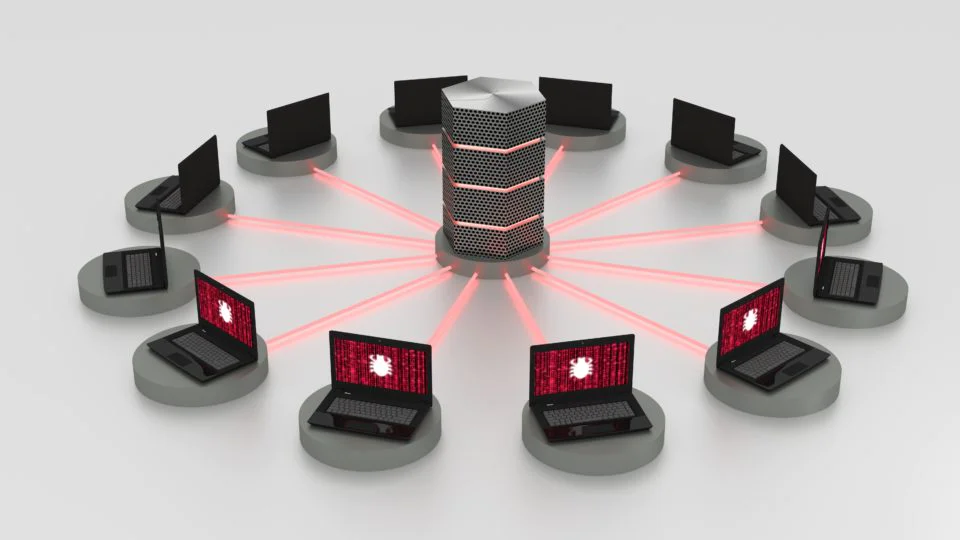
Botnets have become ubiquitous in today’s contemporary anti-abuse and digital messaging landscape. In their simplest form, botnets are individual PCs that have been infected with some form of malware and controlled by an individual. The individual who owns the PC may not realize that their machine is infected. The infection could be completely transparent to the user, or it could be debilitating as more of the computer’s resources are directed toward unseen background functions.
The operator of a botnet will often use the collective computing power of a botnet to launch things like a denial of service attack (DDoS) or turn each of the individual machines into a mini email server to send small amounts of spam. Since the volumes are small, they can fly under the radar, but thousands of machines together represent a sizable attack vector to an ISP/domain. Since each machine may have a different IP, the domain that the botnet operator uses, and the content of the messages, becomes the only method by which these pieces of spam can be identified and blocked—hence the importance of domain-based reputation.
Pro Tip
Learn more about domain reputation in Luke Martinez’s blog post, What is Domain Reputation and Why is it Important?
Legitimate mailers need to be aware of botnets and their attack signatures—using multiple ESPs, or spreading email across too many IPs can manifest as a quasi-botnet attack, more probably like a snowshoe attack (discussed below). Marketers may employ multiple IPs to ensure throughput and the spreading of complaints, in addition to the separation of brand-based reputations and other logical segmentation criteria. But keeping the IPs contiguous (all the IPs in a single netblock and in sequence) can help to differentiate the traffic from that of a botnet and ensure an ongoing healthy reputation.
Botnets are hard to identify—to dismantle a botnet, authorities need to locate the command and control server used to direct the actions of the bots (PCs), which may or may not lead to the botnet operator. Generally there are layers of obfuscation and misdirection between the bots, the command and control server, and the operator to make the dismantling and mitigation efforts of anti-spammers and law enforcement infinitely more difficult.
Chapter 4: Doxxing and Swatting
Doxxing
Doxxing isn’t necessarily a messaging abuse strategy or specific attack, it is however related to subscription bombing because it’s the act of outing someone’s personal information (addresses both physical and Internet) so that like-minded actors can abuse the individual. When you stop and consider the 2016 subscription bombing attacks, these were targeting specific, individual email addresses that were enrolled in hundreds of different lists. A person’s private email was effectively “outed” and subjected to abuse.
Swatting
Swatting is the act of making a hoax call to authorities to get them to show up at someone’s house. This was most famously done by a spammer who tried to retaliate against Brian Krebs, an infosec investigative journalist. The spammer sent pure heroine to Krebs’ house and then spoofed a call from a neighbor to local PD.
These two attacks are both forms of Internet abuse that have found their way into wider and more pervasive forms of malicious digital activity. Oftentimes they have some kind of messaging vector associated with them, but are not pure email attacks by any stretch.
Chapter 5: Joe Job
According to Wikipedia, a Joe Job originated in 1997, when a user under the joes.com domain was cut off for abusive practices. In retaliation, the user spoofed joes.com and sent a massive spam run where the reply-to was joes.com. Typically a joe job spoofs someone’s domain and redirects the abuse back at the spoofed domain. The resulting flood of bounces, blocks, and other feedback signals can act like a denial of service attack or massive nuisance as the recipient servers do what they’re trained to do: prevent abuse from reaching their end uses and redirecting notifications of the block to the purported originator.
DMARC is a good way of mitigating these kinds of attacks because it instructs a connecting domain what to do with email that fails an SPF/DKIM check (which most likely will fail if it’s set up correctly). The owner of the DMARC record could simply tell the receiving domain, if SPF and DKIM fail, then please drop the mail, discard it, it’s fake, and sending me bounces is not necessary. Instead, the owner of the DMARC record could request forensic information to alert them of the attempted fraud and do his or her own analysis on the abuse.
Chapter 6: Phishing, Spear Phishing, and Cousin Domains
Phishing

Phishing might be one of the most common and widely known forms of messaging abuse on the Internet today. In the most simple terms, phishing is the act of trying to fool someone into revealing their password or other sensitive information so that a hacker or spammer can take over their accounts, make purchases using their financial information, etc. The typical way an attack like this occurs is that a known brand or website is spoofed and messages that look like they came from a known entity are sent.
The messages are spoofing the brand’s domain and the content has been engineered in such a manner that its goal is to fool the recipient to believe they are legitimate. The typical language goes something like this: “Dear User, your account has been limited! Please log in to re-enable your account.” Numerous companies employ first and last name personalization to help differentiate their legitimate messages from fraudulent ones.
Your bank will never ask you to log in or provide your log-in information electronically.
Technologies such as two-factor authentication have also been helping curb the tide of attacks such as this by creating a close loop system to establish identity and authenticity.
Technologies such as SPF, DKIM and DMARC help a company protect their brand (and specifically messaging domains) from abuse and implication in phishing attacks by linking the domain to its specific sending IP through SPF. DKIM ensures that the content is intact through cryptographic keys while DMARC provides a set of instructions to the receiver on what to do if the message fails authentication (e.g. discard it because it is spam or phish).
Spear Phishing
What differentiates spear phishing from phishing is the targeted nature of the attack. Spear phishing is usually associated with the CEOs and other high ranking corporate officers at a company. Spear phishing is the unique and targeted application of social engineering to obtain passwords and other sensitive information that could lead to the compromise of large volumes of customer data and/or millions of dollars in company funds and revenue as revealed last fall in the spear phishing hack of Matel.
Cousin Domains
If a company successfully locks down its messaging domains and provides a reject flag in their DMARC records so that fraudulent messages attempting to spoof their brand are dropped by a receiver, they can still be the target of a cousin domain attack. Cousin domains or look-alike domains are exactly what they sound like: domains registered by spammers that look like a legitimate domain, e.g. g00g1e.com, amazoin.com, bannnanarepublic.com, cc-info-security-paypal.com.
These domains are hard to detect because they are not trying to send messages as the legitimate domain. Instead, attacks using cousin domains are leveraging the brand’s look and feel and hoping to dupe someone into disclosing a password or other information. When a cousin domain is detected, the registrar of the domain is often contacted informing them that such a domain exists and asking them to take it down so no more messages can be sent purporting to be from that domain.
Chapter 7: Ransomware

In its simplest form, ransomware is a form of malware that is downloaded to a local computer from a virus-laden email or through a compromised web page that could be linked from an email. Once a ransomware package infects a computer it has one of two basic purposes:
1. Encrypt and hold the contents of the computer hostage (rendering it useless and inaccessible) until such time as the owner of the computer pays the operator of the ransomware through some electronic means.
2. Threaten to publish the contents publicly thereby “doxxing” the owner and their computer’s contents.
Pro Tip
Learn why you should avoid using link shorteners in our blog post, Link Shorteners are Great…But Not For Email.
Ransomware attacks have increased in frequency—they are particularly damaging in a day and age where so much of our professional and personal lives are online or contained in an electronic format. Oftentimes link shorteners are employed to obfuscate the redirect or underlying link that leads to the download of ransomware onto a machine.
A cross industry/law enforcement effort called NoMoreRansom.org has been providing solutions for victims of ransomware, fingerprinting, and creating unlocking mechanisms. NoMoreRansom is the brainchild of Europol, the European Cyber Crimes Division of Interpol.
Chapter 8: Slow Loris
The slow loris might be one of the cutest creatures on the planet, however, this article is not celebrating the animal kingdom, otherwise I’d wax poetic about loris’, sloths, and koala bears. The “Slow Loris” attack refers to a method of ramping up connection and throughput by sending small quantities of email, similarly to how a legitimate ESP builds reputation on a new IP (otherwise known as IP warmup) until such time that the spammer can cram a ton of email through the connection until it is shut off entirely. Once that happens, the spammer will switch to a new IP/domain combo, perhaps slightly tweak the content to try and circumvent content filters that are now looking for his email’s fingerprint, and repeat the attack.
ISPs publish their connection rates and throughput limits as a means of helping mitigate the flow of inbound email. Every ESP in the world knows what these connection rates and throughput limits are and complies with this technical standard. If an ESP is not respecting their connection limits, then their traffic begins to resemble that of a spammer and an ISP is more likely to route mail to the spam folder or block it outright.
Chapter 9: Snowshoeing
Spamhaus has a very succinct definition of snowshoeing on their site. The idea of a snowshoe attack is spreading complaints and volumes across a broad range of IPs and domains. You may be thinking to yourself, “I’m a legitimate marketer and I use multiple IPs for sending my email. Am I a snowshoer?” No, you’re not. If you’re following all applicable best practices, then using multiple IPs is a standard way of achieving the necessary throughput you need to deliver email in a timely fashion. Oftentimes, ISPs have connection and throughput limits per IP and an ESP may also have their own limitations.
Adding IPs to scale outbound traffic has been a feature of ESPs for a long time. What differentiates how ESPs spread traffic vs. how a snowshoer spreads their traffic has to do with the use of domains. A spammer will want to obfuscate as much of the traffic as possible to make it more difficult for an ISP or receiver to block them. Legitimate mailers use consistent domains with published email authentication records to establish their brand’s reputation and to protect it from spoofing and abuse.
As you can see, it’s fairly easy to go from a good legitimate sender to a spammer if you don’t apply all the necessary forms of email authentication to your outbound email.

Subscription bombing is a relatively new phenomenon, or one that came to prominence recently. Spammers have realized that they can render a person’s email account null and void by leveraging the subscription forms hosted by ESPs. The typical way they do this is to subscribe a single account hundreds of times across ESPs so that it begins to receive massive quantities of email. The end result is that the individual owner of the account finds him or herself drowning in email they never signed up for.
One of the more high profile targets of this spate of recent attacks that began in the summer of 2016 was Brian Krebs, a technology journalist who has devoted a massive amount of time and resources to hunting down spammers and other digital miscreants.
Essentially, subscription bombing was a kind of doxxing attack—it targeted specific accounts and used bots to sign up en masse through insecure, non-CAPTCHA protected subscription forms. Not only were individuals abused by this attack vector, but ESPs that didn’t employ a CAPTCHA became unwitting tools in this specific form of abuse. The recommendation since this transpired was to use a form of CAPTCHA in protecting a signup form from automated signups by bots and other ne’er do wells.
Pro Tip
Learn how to protect your sign-up forms on our blog. The recommendation since this transpired was to use a form of CAPTCHA in protecting a sign-up form from automated signups by bots and other ne’er do wells.
Additional countermeasures include using a confirmed opt-in strategy. In this case, even if the bot were able to subscribe someone, the volume of email would stop at 1, until the individual completed the opt-in process manually. Or give the user an easy method to opt out, without suddenly unloading a massive amount of email into their account.
Chapter 11: Waterfalling
Waterfalling describes the practice of moving their traffic from one ESP to another in order to achieve maximum effect. A spammer will take a stolen list and then “wash” it by sending it through a smaller ESP that may not have the tools and technology to assess the risk of a particular client through proper vetting. The same list will then be sent through another ESP and then another ESP, improving its value and efficacy with each pass until it is either sold or completely burned out.
Typically, the IPs that the spammer uses at each ISP will become list denied and most likely unusable. Usually a spammer will focus their efforts on smaller, mid-tier ESPs, avoiding large ones due to the upfront costs to deploy. However, it is not uncommon for a legitimate, or what is sometimes referred to as a graymail sender (a sender that barely toes the line of legitimate email) to employ multiple ESPs to spread their traffic as widely as possible thereby appearing to snowshoe (in the case that they use similar domains).
It might sound like employing multiple ESPs is always a bad thing—it isn’t necessarily. Sometimes the fact that a large company uses multiple ESPs is a byproduct of acquisitions and large organizations that results in messaging sprawl. Different stakeholders within an organization may choose to use different messaging platforms to deliver email thereby creating a large messaging footprint. As long as each stream employs best common practices, the overall reputation of the sender should remain high and positive.
Appointing someone to have central and critical oversight across all the various messaging streams will create the kind of continuity that leads to improved reputation and increased inbox performance, not to mention the ability to more quickly react to delivery issues.
Chapter 12: Conclusion
The universality of email has connected the world in unimaginable ways. Similarly, it has created unforeseen vulnerabilities across a broad spectrum of systems and businesses. According to studies by the Messaging, Malware, Mobile Anti-Abuse Working Group (M3AAWG), over 90% of all email traffic directed at an ISP or mailbox provider is spam. Legitimate email makes up a fraction of the total global volume of email. So the lopsided relationship between legitimate email and spam puts the onus on the world’s biggest brands and senders to ensure that their strategy and systems are differentiated from spammers every step of the way.
This guide is meant to provide context on how certain legitimate marketing tactics can appear to be similar to the approach taken by spammers when viewed from the perspective of an ISP or mailbox provider. This guide is in no way a handbook for fending off deceptive practices—today’s digital marketers are wearing both creative and technical hats. The marketplace is fractured and complicated so it behooves us all to know and understand the kinds of perils we face in our daily jobs.
Learn More
For more information about email and email best practices, check out our 2017 Email Deliverability Guide.