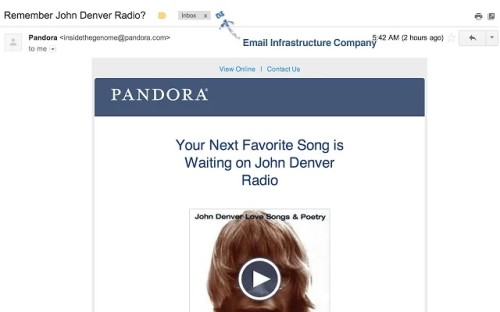
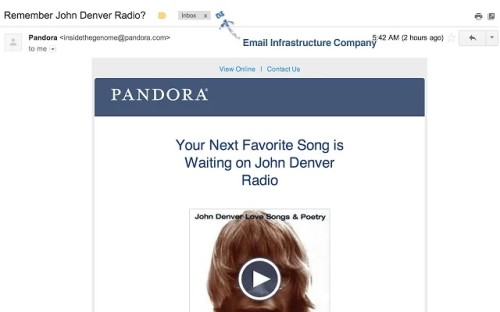
Since you’re reading the SendGrid blog, it probably won’t surprise you many companies turn to email infrastructure services to send their email, rather than
building your own. As an employee of one of these infrastructure companies, I’m always interested in finding out what company is behind the email getting sent. To do this I wrote a
Chrome Plugin that attempts to determine what company sent the email. In writing the plugin, I learned a lot about how to determine what company sent an email, a process I wanted to share.
Most email infrastructure companies identify themselves in email headers, many of those, through proprieatary X-Headers, identifying users, or email ids. Others will identify themselves in their DKIM, X-Mailer, or other headers. Still others don’t identify themselves at all and you must recognize patterns.
Some of the fingerprints I found are as follows. In identifying fingerprints, I only chose one identifier, which I found were the easiest to identify and the least likely to be copied or accidentally end up in emails that were not sent by the infrastructure company. Often, companies have multiple points fingerprinting them,
those are not included, if you wanted more precision you might need to look at all points.
Many email senders will include non standard X-Headers, that better identify the email or the user sending it. (We use
X-SG-EID: YOUR-EMAIL-ID). The companies I’ve seen do the following:
- Amazon SES - X-SES-Outgoing
- Constant Contact - X-Roving-ID
- Dyn - X-DynectEmail-Msg-Key
- Email Vision - X-EMV-MemberId
- iContact - X-ICPINFO
- MailChimp - X-MC-User
- Mailgun - X-Mailgun-Sid
- Mandrill - X-Mandrill-User
- Marketo - X-MarketoID
- Postmark - X-PM-Message-Id
- Responsys - X-rext
- Salesforce - X-SFDC-User
- SendGrid - X-SG-EID
- SMTP.com - X-SMTPCOM-Tracking-Number
Some companies expose their information in other, non proprietary headers, a sample is as follows:
- Bronto - Found in the DKIM-Signature header, d=bronto.com, this really communicates that the sending email is @bronto.com, but in all emails I profiled of known Bronto senders, that was in fact the case.
- Listrak - In the Received header, listrak.com is listed.
- Mailjet - Also found in the DKIM-Signature, s=mailjet.com identifies Mailjet.
Some mail services do a really good job of masking the fact that they sent an email, but still have some sort of pattern that allows identification. These often are subtle and can be duplicated easily by others (so are imperfect).
- ExactTarget - In the x-job header (note the lower case), jobs follow the pattern of {DIGITS}_{DIGITS} (e.g. 118714_56000708) additionally, found in the first Received header, mta{DIGIT(S)}.email.{DOMAIN} (e.g. mta2.email.thinkgeek.com)
- Silverpop - Found in the first Recieved header, {SUBDOMAINS}.mkt{DIGITS}.com (e.g. mail4098.istockphoto.mkt2173.com), additionally all second level domains (e.g. mkt313.com) contain a link to abuse@silverpop.com.
You can find out much more about your email, by looking it up in
SenderBase. However for on the go fingerprinting, this should get you going.
This list is by no means comprehensive and will certainly change. To find up to date fingerprints (and potentially more), check out
the GitHub project for Email Intelligence. If you know of more fingerprints, please don’t hesitate to make a pull request.